Abstract
Sovereign-T3 Protocol emerges as a groundbreaking blockchain
solution that seamlessly integrates Self-Sovereign Identity (SSI) into
its core architecture, providing users with unprecedented control over
their personal data and establishing a secure foundation for a multitude
of applications. This EVM-compatible blockchain fosters a decentralized
ecosystem where smart contracts play a pivotal role in revolutionizing
identity verification processes, from birth and death registration to
academic and professional journey tracking. This explanatory note delves
into the core principles, technical aspects, and potential applications
of the Sovereign-T3 Protocol, showcasing its potential to
reshape the landscape of identity management and decentralized
applications.
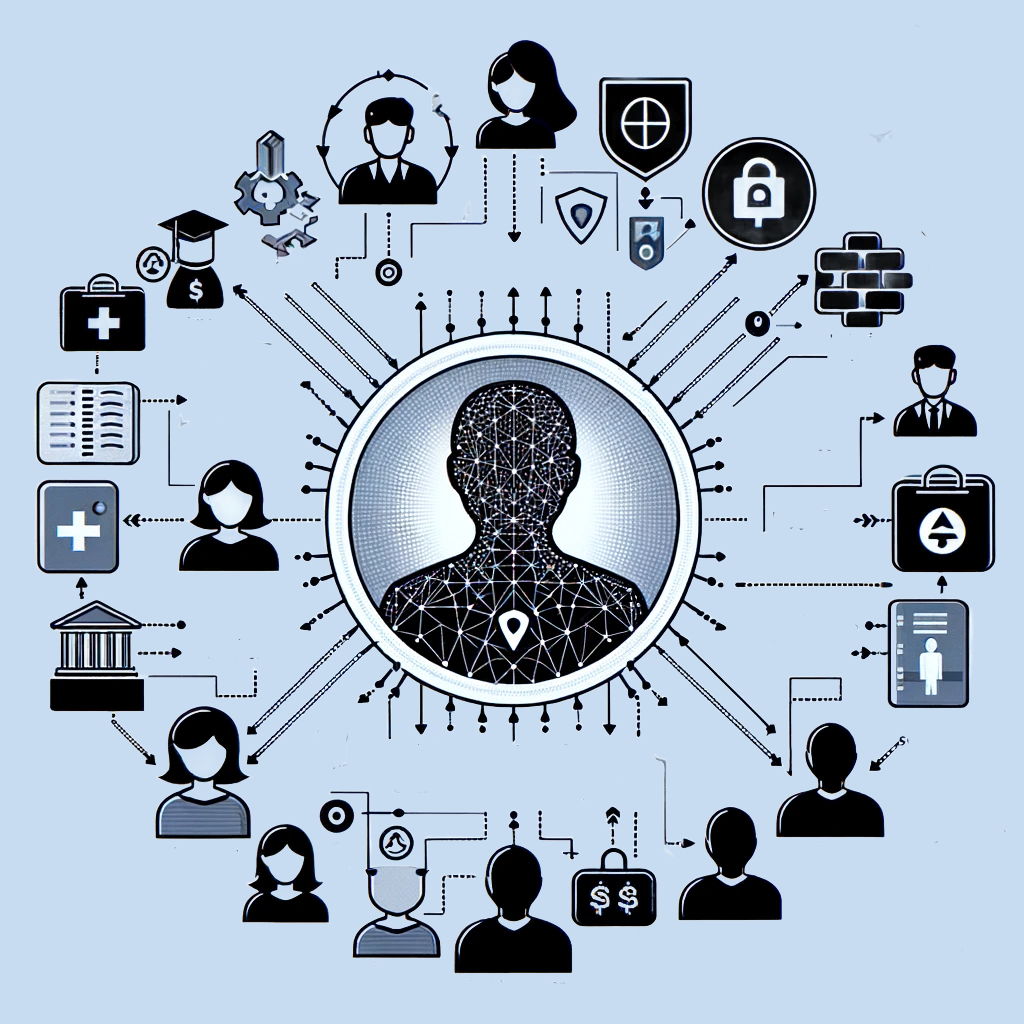
A graphical representation of a Self-Sovereign Identity (SSI) enabled
blockchain ecosystem Sovereign-T Protocol. In the center, depicts a
user who creates or is issued a Decentralized Identifier (DID). Around
the user, shows various agents like schools, universities, hospitals,
corporates, NGOs, and microfinance institutions, each with their own
graphic symbols representing DIDs forming a circle around the user. It
Illustrates interactions between the user and the agents (various
institutions) using lines or arrows, showing a new DID that is created
in the form of a transaction hash generated on the Sovereign-T
Protocol. This interaction serves as proof of interaction within the
system. Emphasizing the ecosystem's ability to keep the user anonymous
while proving credentials within the system for different agents. The
design conveys privacy, security, and a user-centric approach in a
decentralized digital identity system.
10 Core Principles of Self-Sovereign Identity (Christopher Allen)
"The 10 Principles of Self-Sovereign Identity (SSI)" provide a
foundational framework for Sovereing-T3 Protocol as well as
understanding and implementing self-sovereign identity. These principles
are designed to guide the development of systems that put users in
control of their digital identities, ensuring privacy, security, and
full personal autonomy. Here's a detailed explanation of each principle:
-
Existence: Individuals must have an independent
existence.
- Control: Users must control their identities.
-
Access: Users must have access to their own data.
-
Transparency: Systems and algorithms must be
transparent.
- Persistence: Identities must be long-lived.
-
Portability: Information and services about identity
must be transportable.
-
Interoperability: Identities should be as widely
usable as possible.
-
Consent: Users must consent to the use of their
identity.
-
Minimalization: Disclosure of claims must be
minimized.
-
Protection: The rights of users must be protected.
Why Sovereign-T3?
The term "sovereignty" traditionally refers to the supreme authority or
power to govern oneself without interference from external sources. In
political contexts, it often pertains to the autonomy and
self-governance of a nation-state. In the context of blockchain
technology, the concept of sovereignty takes on a new and powerful
meaning, aligning with the core principles of autonomy,
decentralization, trust, and transparency that blockchain aims to
achieve. Blockchain technology, at its essence, seeks to provide a
decentralized and trustless system where individuals have greater
control over their data, assets, and interactions. Let's break down how
the concept of sovereignty manifests in the core principles of
blockchain:
-
Autonomy: In a blockchain network, each
participant has autonomy over their own actions and assets. Smart
contracts, which operate based on predefined rules without the need
for intermediaries, enhance this autonomy. Participants have control
over their transactions and can engage in peer-to-peer interactions
without relying on a central authority.
-
Decentralization: Sovereignty is closely
tied to the decentralization aspect of blockchain. In a decentralized
network, there is no single point of control or failure. Participants
collectively contribute to the governance and maintenance of the
network, ensuring that decisions are made through consensus rather
than by a central authority. This decentralization promotes
sovereignty by distributing power across the network.
-
Trust: Blockchain's distributed ledger and
consensus mechanisms contribute to trust within the network.
Participants can trust the system's integrity, as the transparent and
immutable nature of the blockchain ensures that once a transaction is
recorded, it cannot be altered. Sovereignty is reflected in the trust
that participants place in the technology itself, rather than relying
on trust in centralized entities.
-
Transparency: Sovereignty and transparency
go hand in hand. Blockchain provides a transparent and auditable
record of transactions visible to all participants. This transparency
enhances the trustworthiness of the system and empowers individuals
with a clear view of the network's operations. Participants can
independently verify transactions and ensure the integrity of the
system.
Now, let's consider the term
"Sovereign-T3" where
'T' stands for Trust,
Transparency, and
Total Autonomy:
-
Trust: Trust is fundamental to the concept
of sovereignty within the context of blockchain. Sovereign-T3
emphasizes the establishment of trust through the inherent features of
blockchain, enabling participants to transact and interact with
confidence.
-
Transparency: Transparency is a key pillar
of Sovereign-T3. The 'T' underscores the commitment to
providing a clear and open view of the network's operations, ensuring
that participants can verify transactions and governance processes
independently.
-
Total Autonomy: The term "Total Autonomy" in
Sovereign-T3 reinforces the idea that participants have
complete control and self-governance over their digital identities,
assets, and interactions within the blockchain network. It
encapsulates the essence of sovereignty in the digital realm.
In summary, the concept of sovereignty is deeply ingrained in blockchain
technology, and the term "Sovereign-T3" further emphasizes
the commitment to decentralized trustless environment, transparency, and
total autonomy within the blockchain ecosystem.
Technical Architecture
-
Consensus Mechanism: Sovereign-T3
Protocol employs a robust consensus mechanism, ensuring the integrity
and security of the blockchain. The consensus mechanism may be based
on Proof-of-Stake (PoS), Proof-of-Work (PoW), or a hybrid model,
providing flexibility based on the specific requirements and goals of
the blockchain network.
-
Interoperability: The blockchain is designed
to promote interoperability with other blockchains, ensuring seamless
communication and data exchange. Interoperability allows users to
leverage their SSI across multiple platforms, enhancing the overall
utility of their decentralized identities.
-
Data Encryption and Privacy: To uphold the
principles of SSI, Sovereign-T3 Protocol incorporates
advanced cryptographic techniques to encrypt and protect user data.
This emphasis on privacy ensures that personal information remains
confidential, and users have granular control over what information is
shared and with whom.
-
Scalability: Recognizing the importance of
scalability in a blockchain network, Sovereign-T3 Protocol
employs innovative solutions such as sharding or layer 2 scaling
solutions. This ensures that the network can handle a growing number
of users and transactions without compromising performance.
The leading framework under consideration to build Sovereign-T3
Protocol is Cosmos SDK as it allows building application specific
blockchains. Application-specific blockchains are emerging as a powerful
tool in the world of blockchain technology, offering several significant
benefits across various dimensions such as flexibility, performance,
security, and sovereignty. These blockchains are distinct in their
approach, allowing developers to tailor their blockchain network
specifically for a particular application, which stands in contrast to
the more general-purpose nature of traditional blockchains.
-
Flexibility: One of the key advantages of
application-specific blockchains is the high degree of flexibility
they offer to developers. In the Cosmos ecosystem, for example, the
state-machine of a blockchain is linked to the consensus engine via
the Application Blockchain Interface (ABCI). This interface is
language-agnostic, meaning developers can build their state-machine in
any programming language. This freedom extends to the choice of
development frameworks as well, with options like Cosmos SDK, Lotion,
and Weave available, each supporting different programming languages.
Moreover, the ABCI allows for the substitution of the consensus
engine. Currently, CometBFT is the primary option, but there's
potential for more in the future. Developers also have the liberty to
fine-tune the chosen framework and consensus engine to better suit
their specific needs. They can make decisions on a range of
trade-offs, such as the number of validators versus transaction
throughput or safety versus availability, and on design choices like
database types or account models. The Cosmos SDK even permits
automatic execution of code at specific times, and developers can
choose their cryptographic library, offering a level of customization
not typically available in virtual-machine blockchains.
-
Performance: In terms of performance,
application-specific blockchains have a distinct edge over
decentralized applications built on smart contracts. Since these
blockchains are dedicated to a single application, they avoid the
competition for computational and storage resources seen in
non-sharded virtual-machine blockchains. The use of efficient
consensus mechanisms like CometBFT, as opposed to the more commonly
used Proof-of-Work in virtual-machine blockchains, significantly
boosts throughput. The primary bottleneck in transaction processing is
the state-machine, and by avoiding the need for transactions to be
processed by a virtual machine, application-specific blockchains can
greatly reduce computational complexity.
-
Security: Security considerations are also a vital
aspect of application-specific blockchains. Developers can leverage
established programming languages like Go, avoiding the pitfalls of
immature smart contract languages. They are not restricted to the
cryptographic functions of underlying virtual machines and can employ
custom cryptography with well-audited libraries. Furthermore, the
absence of an underlying virtual machine reduces the risk of bugs or
exploitable mechanisms, simplifying the security analysis of the
application.
-
Sovereignty: Perhaps the most significant advantage
of application-specific blockchains is the sovereignty they provide.
In a decentralized application ecosystem, various actors are involved,
including users, developers, and third-party services. When
applications are built on shared virtual-machine blockchains, the
community of the application is often overshadowed by the community
governing the underlying blockchain. This misalignment can lead to
challenges in updating or fixing the application if the broader
community is unresponsive. Application-specific blockchains solve this
governance misalignment by granting full control to the stakeholders
of the application over the entire chain. This ensures that the
community is not immobilized by discovered bugs and has the freedom to
evolve as it sees fit. This level of sovereignty is crucial for the
long-term viability and adaptability of decentralized applications.
For a comprehensive understanding of the Cosmos SDK and to gain insights
into the nuances of application-specific blockchains, as well as to
explore the limitations inherent in Smart Contracts-based ecosystems
such as the Ethereum Virtual Machine (EVM), visit
official cosmos SDK docs





